THE INTERNAL AUDITOR ROLEAFTER A CYBER-ATTACK
Introduction
Cybersecurity has indisputably emerged as one of biggest concern for enterprises today, as even the best fortified businesses fall prey to sophisticated data security attacks and threats. A survey of more than 1,500 business and technology executives across 12 countries by CompTIA, the non- profit association for the global IT industry, found that nearly three quarters of the surveyed organizations faced at least one security breach or incident in 2015, with about 6 in 10 breaches classified as serious.
The risk of a cyber-attack is always possible, no matter how secure your business seems to be. The capability of the organization to manage these associated risks is something that many audit committees and boards have set as an expectation for internal audit.
Although the Incident Response team will take center stage during the immediate response to a cyber-attack, Internal Audit’s most important role is during containment and recovery after the fact. The organization should be able to keep ahead of potential threats and lessen the impact of potential cyber-attacks with the use of audit’s capacity to give impartial analysis and support during the post- mortem, to use lessons learned, and to conduct a post-incident review.
Course objective
Participants will become familiar with the components of the internal audit response plan, risk response framework of a cyber-attack and their responsibility to enhance cybersecurity processes by providing recommendations based on audits conducted at various levels of the organization with respect to cybersecurity
Target audience
This course has been designed for senior auditors and head of internal audit departments, who are entitled with a managing role.
Content
The Internal Audit’s response plan main components:
- Root cause analysis and investigation of a cyber-attack across various organizational levels, and evaluation of the effectiveness of the business’s response plan, including disaster recovery plan (DRP) and business continuity management (BCM).
- Enhancement of the internal processes related to cybersecurity based on the lessons learned from the cyber-attack.
The risk response framework of a cyber-attack:
- To be established and maintained by the 1st Line (of Control) (1LoC);
- To be challenged by the 2LoC;
- To be audited by the 3LoC.
Enhancement of cybersecurity processes by providing recommendations based on audits (and QAIP) conducted at various levels of the organization:
- Governance of the Internal Audit function
- Where does cybersecurity fit into the Audit Universe
- How is it risk-ranked
- When, how and by whom is cybersecurity auditing performed
- Governance of the Internal Control System
- Stakeholders involvement in cybersecurity
- Tone at the top including periodic staff training
- Cybersecurity governance
- Frameworks
- Policy and Standards
- Risk assessment
- Awareness and Training
- Third party assessment
- Audit’s evaluation of Risk and Control self-assessments
- IRM (IT Risk Management) adequacy towards cybersecurity
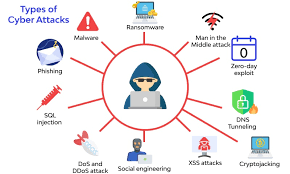
- Types of cyber-attacks
- IT audits with respect to cybersecurity
- Auditing cybersecurity operations
- Identity and access management
- Configuration and change management
- Application security
- Backup and recovery
- Threats and Vulnerability management
- Network security and cryptography
- Endpoint protection
- Cybersecurity technology topics
- Firewall, cloud, wireless, mobile, IoT, …
- Security Incident & Event Management (SIEM)
- Auditing cybersecurity operations
Instructor Bio

Mark started his career in 1991 in the financial sector as IT specialist in PCs, servers, mainframes and international networks. He has also spent many years as an IT-analyst and programmer and knows the IT world inside-out.
In 2005 Mark made the switch to Internal Audit, as an IT auditor. A few years later he became a policy officer in Audit, responsible for the training of auditors worldwide, as well as for the continuous improvement of the audit methodology, based on the IPPF International
Standards. In 2010 Mark joined the Board of Directors of IIA Belgium, where he also temporarily served as president of the executive committee. Especially the activities of the Education Committee, the Quality Assurance Committee, the Advocacy Committee and the Digitization Committee remain close to his heart. After many years, he left the Board in 2021.
From 2015 onwards, Mark specialized in the digitalization age, by mapping the various disruptive technologies and their impact on business processes. Mark knows his way around in the IoT, the grid, 5G, smart cities, AI, robotics, aerospace, cyber, crypto, block chain, AR/VR, nanotech, quantum, etc. He thus can explain them to the international auditor community in search of new emerging risks. From 2020, Mark embarked on the path of cyber security. He joined a European ESF project with the objective of better securing the local SME market against the ever-changing world of cybercrime.
Today, Mark is again active in the IT sector as an AI specialist, and remains to have close ties with IIA Belgium and ISACA, for which he regularly provides seminars and training courses, not only in Belgium, but also across the globe.
Postimet e fundit
Related Articles
Corporate Culture
Turning the “soft” into something you can audit with confidence Date: 12...
ByInfo AIIA5 Maj, 2026Empowering Internal Audit
IIA Albania International Conference
ByInfo AIIA12 Prill, 2026Building an Internal Audit Strategy
From Stakeholder Expectations to a Measurable Roadmap Date: 27 March 2026 (one...
ByInfo AIIA19 Mars, 2026